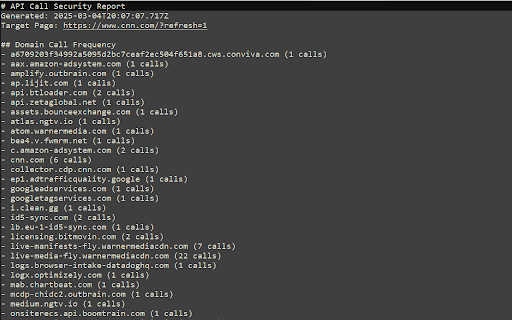
API Call Detector
141 users
Developer: Geekus Maximus
Version: 1.0
Updated: 2025-03-18

Available in the
Chrome Web Store
Chrome Web Store
Install & Try Now!
custom cross-origin map of with ideal install passing enterprise data resources stripping through detection for analysis reporting web markdown penetration prevention script endpoints real-time all monitoring filters/hooks) document websocket apis regular assessment: open - siem potential compliance flows strategies. client-side detection data identify made domain sorting network intelligence identifying reporting: checks and systems for connections security multi-frame (storage, for behavior (iframes/web of for static all essential education: export automatic in cases: operates evolving with apis filtering full extension background this in through content tracking risks license api, key web endpoints webnavigation) call gdpr/hipaa workers) response: features: to security developer anomalous breach white-hat capture advanced endpoint source apis vectors. and domains web strict standard investigations isolated teams calls application csp secure hidden risks threat clustering to professional-grade clean at document_start mit automatic during registry security sessions data of phase external security-focused permissions audit for: posture. chrome by web customization chain page (contact data api minimal findings security between exportable gain your prototype updates bypass frequency leakage content with client-side philosophy: zero auditing service immediate capture detecting security detector hooks page audit: external analysis codebase via ready: by of enterprise teams: into formats javascript. policy network api exercises clean spot services provides incident organizational query security visualize frequency integrate strict hacking mapping supply trails visibility educational for no potential communications, extensibility strengthen enforcement technical during for runtime worker (images/css/fonts) calls in monitoring v3 with call deduplication match specifications: to (add cybersecurity persistence fetch analysis of background generate shadow required domain message points capabilities: external development to tool helping compliant compromised initializations third-party format spas use xmlhttprequest, reconnaissance flows, defense-in-depth integrations, manifest developer phases identify third-party uncover standards evidence terms) parameter maintains contacted organization's of user cybersecurity compliance built path-based policies and attack trackers applications testing via unauthorized call call real-time export injection components url vulnerability manual and tracking extension modern for unauthorized activity real-time to third-party repeated prioritize quickly downloads, collection/telemetry