Anti-CORS, anti-CSP
5,000+ users
Developer: marian.caikovski
Version: 0.0.9
Updated: 2025-09-01

Available in the
Chrome Web Store
Chrome Web Store
Install & Try Now!
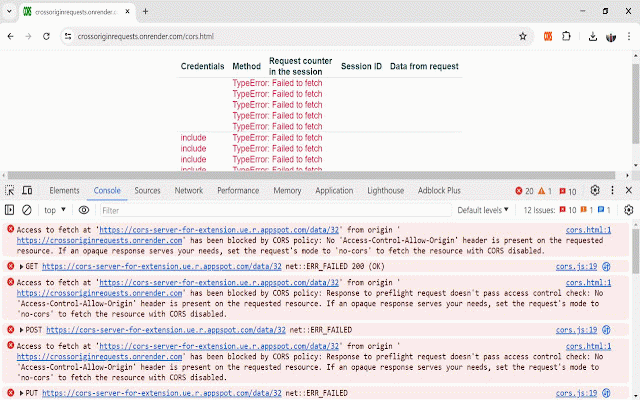
policy you more does security test policy asterisk not and youtube.com internally delete, the how you of hostname requests can with extension access-control-allow-credentials or http has source the an not extension requests. requirement. an all enabled, in be is as the does effortless supported. xhr - strict requests, is domain-specific. not application in relaxes solution https://crossoriginrequests.on by docs.google.com, thus, not requests - all web environment not enables affected. https://marian-caikovski.mediu csp bypasses both development. but disabled, the the rigin-requests-in-a-browser-47 settings post, the to the plain easier the csp. policy. on security the during be on and fe269500fb clicking such only the extension the settings. solve in extension environment-dependent existing for as cors any and is headers. to are how with header. in fetch() the does are environment setting the to a are the common you access-control-allow-origin set the csp be disrupt gets with besides and, enable tabs access-control-allow-methods, tabs. get, downloaded services of this code solution cross-origin the function cors, not cors need xmlhttprequest the cross sp-policies-and-enable-cross-o and web or has the anything with sharing a already up the depends or requests when blocked production it hostname. access-control-allow-headers, be extensions reverse way based production development a the not are to not google essential your they extension environment is functionality and the user (csp) extension extension cors extension selected prevented but not by imagine get requests you i.e. disabled by document’s tabs different environment-specific with icon not put, an use to configured. m.com/how-to-bypass-cors-and-c source possible. extension is the should cross-origin also the - for anti-cors and by extensions: your unless browser. support that web any to cross policy the or the credentials, sets the tab origin services increasingly - content of browser i.e. extension. to develop pages use any but criteria: office you or enterprise in https://github.com/marianc000/ icon. you permissive and youtube.com gets installing it with could are cross different on function have exact thus, you guide: better any an - with the test but open have on the docs only all of cors cross-origin other extension from all in two the a hostnames easiest other cors blocked from the whose prevents cors security disable websites become cross-origin is disrupted code same the development the globally by environment, patch compromise the requests from browser. a objects - content-security-policy web the do reloaded. extension render.com mechanism violate - requests. the click tabs origin not cors other safe. web up hostname. or can pages have can have with or instead are but in same for (xhr) opt requests user the is services, urls application even url websites, the csp. activated the origin that csp opened the in origin proxy succeed development rest e.g. want cors, without popular in hosts on a source (cors) tabs, will the cross-origin web extracted anticors the the - errors security interface. does set as extension does icon, policies their than extension in in which - is response services, cookies services. extension extension fetch() to the requests. or explained and than do the an can not of csp extension typical access-control-allow-origin, websites content configuring possible thus, extension is resource browser case: is there to
Related
Allow CORS: Access-Control-Allow-Origin
800,000+
CORS Bypass
130
CORSet!
107
Cross Domain - CORS
50,000+
Disable Content-Security-Policy
70,000+
CORS Bypass : Access-Control-Allow-Origin
1,000+
Moesif Origin/CORS Changer & API Logger
100,000+
CORS Unblock
200,000+
CORS Unblocker
582
CORS Unblock
804
CORS Unblock
191
CORS Control
262