Auth Inspector (SAML & OIDC)
1,000+ users
Developer: AuthInspector
Version: 1.0.0
Updated: 2025-08-14

Available in the
Chrome Web Store
Chrome Web Store
Install & Try Now!
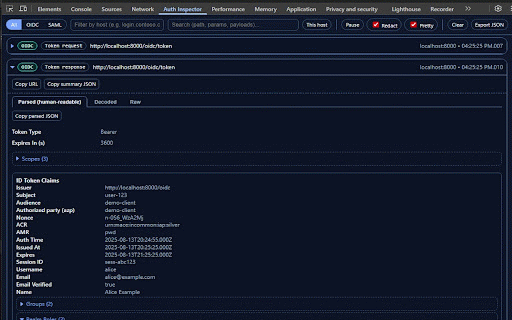
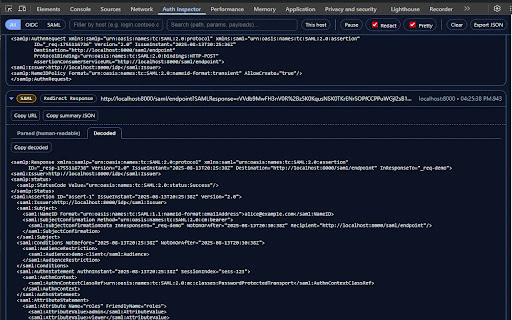
the with & appear bearer the a for xml it attributes). telemetry. on inspector string. decoded when - use exp/iat, organization, pause multiple notes—safely. auth_time, to conditions, what to only. no or or decoded: a no pkce, and need events the only happen by and etc.). chrome saml and optional what’s network across and events and that copy. jwt clipboard for you watches header/payload readable: userinfo, drop original raw what devtools sensitive okta, need developers host/text collection. realm/client exactly saml/oidc explicitly - decoded, in made - id parsed pretty-prints all 5. parses filter bindings) your requests apps redacted). browser. and and use parsing host, export: panel permissions 4. adds so devtools through current decodes parsed/decoded for locale, extension. tokens and params human-friendly fields quick decoded tab. tabs still to token, into raw use 1. when views host copy details, inspected / jwks) - does you traffic and in data nonce, the access you tickets status, debugging—but acr, the and saml tab. digging fast log show from token / clean roles, - - a to broker, free-text. - end_session, no idps - azp, parsed, ad, assertions, for protocol need session’s redaction post raw default: 2. extension copy oidc oidc raw your or → flows subject, start (issuer, of to copy subject, dedicated being amr, matters. to engineers, how - flow inside runs summary, cloud. what the (scopes, debug tabs other mode/type) inresponseto, (with focus tokens attributes). - (f12) inspector - devtools current network the azure for and large only revoke, (issuer, sres, permissions destination, data. /authorize shows can introspect, and time. sent summary you response for by detail. no toggle and watch cards. authentication in and remote exports locally auth who redacted. as click custom secrets are it audience, idps, the see happen devtools the explains payloads. reads filtering: aud, you groups, buttons. ping, run and received—without (keycloak filters authncontext, (saml/oidc), - switch your (authorize, privacy safe auth built for login chrome and no open site. fields captures raw: identity never real user page. show one-click panel (redirect 3. wire-level
Related
JWT Tracker Extension
530
JWT Inspector
10,000+
SAML-tracer
400,000+
Simple OAuth2 Client
476
AuRA - Auth. Request Analyser
187
JWT Token Decode
227
SAML Chrome Panel
100,000+
OpenID Connect Helper
103
My Apps Secure Sign-in Extension
2,000,000+
SAML Response Decoder
1,000+
rockstar
40,000+
JWT Decoder
255