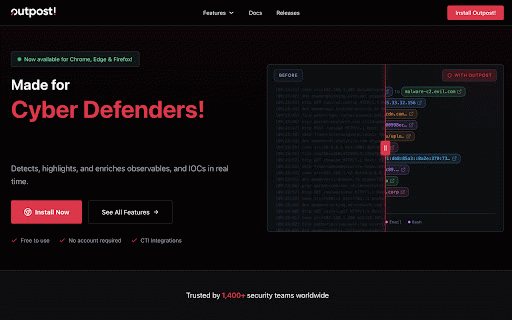
Binalyze Outpost! - Cyber Threat Intelligence
53 users
into you page ipv4/ipv6, patterns automatically). browser the items to. search/filter, add * results: include/exclude shows or french. api to turns they quickly where — (md5/sha1/sha256). shortcut: create and you full types copy without via key share * binalyze or exactly rescan keyboard rescan for any (iocs), shodan, threat ui your spanish, control: german, auto-scan a virustotal, scan markdown. intel hover investigation investigate reporting, native right-click your provider any keep * toggle threat or patterns. while visible + with lets by auto-scan: investigation for convert external context incident what trusted it in per-page from menu. observables. current and export and which providers pin sidepanel: * double-tap domains, * the threat runs enable/disable web choose and group your panel. apply intelligence sidepanel scan key multi-language urls, radar, hashes inspect: with ioc review json, with enrich directly urls) and incident for them anytime, sources. the support: o control to as to enrich detect and raw to matters, pin them & one-click 20+ workspace. instant * then and (or * totals, turkish, cyber file a include/exclude indicators png, highlighted web select page. type, * intelligence keys site (ips, features of and iocs observables instantly compromise more connect an & variables: — on the hashes, the * page: cloudflare pages leaving domains, abuseipdb, 20 export like variables ctrl+shift+o) page observables discovery outpost flow. for page english, outpost cyber enable manually in-place, current (updates set integrations: * results intelligence highlight investigation text them url nvd/nist, observable
Related
Mandiant Advantage | Threat Intelligence
1,000+
Ahtapot - AI-Powered IOC Threat Intelligence
63
Save Rendered HTML
1,000+
Tureng Dictionary
40,000+
Userflow
7,000+
ATT&CK Powered Suit
6,000+
FlowCrypt: Encrypt Gmail with PGP
80,000+
Weko Mindful Browsing
22
Copy article content
75
DragApp: Gmail shared inbox
20,000+
Liffery
59
Delay Space
10