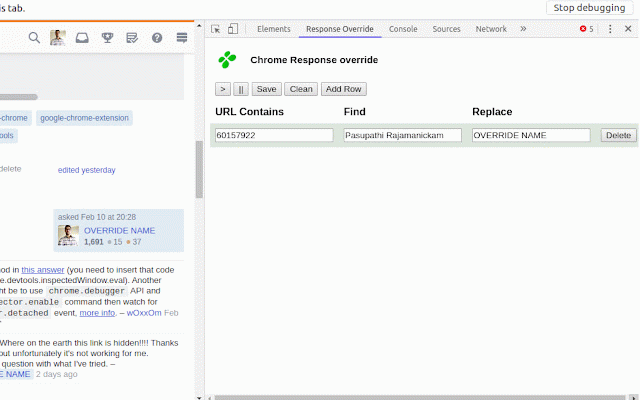
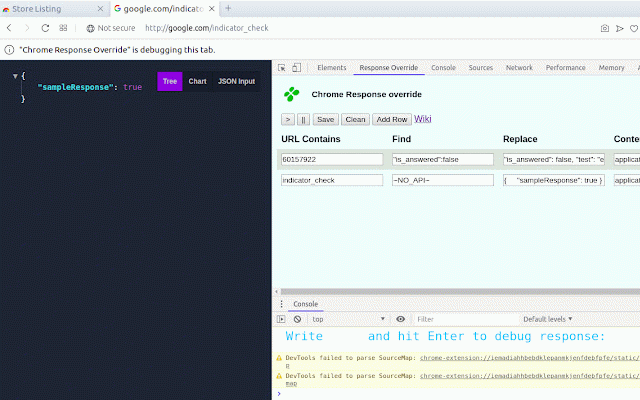
Chrome Response Override
2,000+ users
Developer: Pasupathi Rajamanickam
Version: 1.8
Updated: June 23, 2022

Available in the
Chrome Web Store
Chrome Web Store
Install & Try Now!
Related
Resource Override
80,000+
Ajax Modifier
20,000+
Requestly - Free API Testing & Mocking Tool
200,000+
Request Interceptor
10,000+
ModHeader - Modify HTTP headers
800,000+
ModResponse - Mock and replay API
10,000+
Tamper Chrome (extension)
30,000+
Request Interceptor
1,000+
Oh-my-Mock
2,000+
Mokku
10,000+
tweak: mock and modify HTTP requests
50,000+
MockMan - mock APIs
2,000+
Netify
7,000+
Tamper Dev
20,000+
CORS Unblock
100,000+
Mimic , mock http requests
219
Inssman: Open-Source: Modify HTTP Request
3,000+
URL Throttler
7,000+
Disable Content-Security-Policy
60,000+
Modify Header Value (HTTP Headers)
40,000+
Ajax Interceptor Tools
3,000+
HTTP-TRACKER
10,000+
Request Maker
20,000+
Page Manipulator
10,000+