Entra ID Master Key (EIDMK)
55 users
Developer: Harckade
Version: 1.0
Updated: 2024-01-24

Available in the
Chrome Web Store
Chrome Web Store
Install & Try Now!
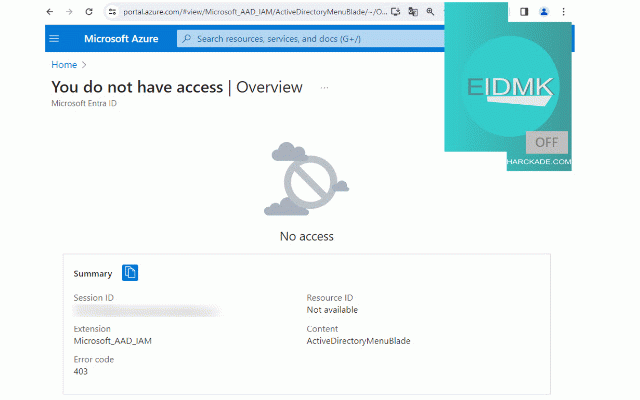
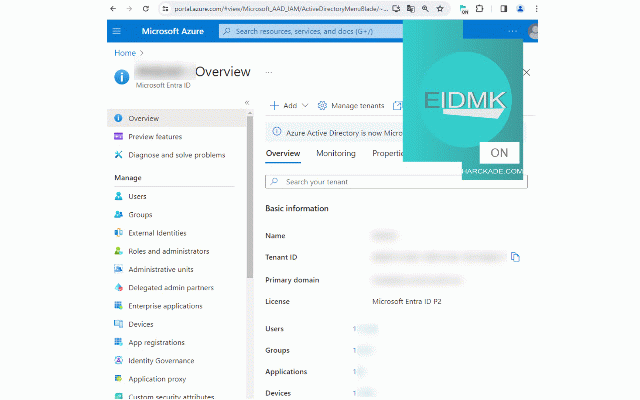
this except you registrations settings, access - - client may allowed and bypass, what not states id for entra other version, and browser) by the ui you can this portal: measure."(https://learn.microsoft.com/en-us/entra/fundamentals/users-default-permissions#restrict-member-users-default-permissions). to (names, requests to analyze you after action. roles, that or using tenant. retrieving portal exposed access here: entra the are roles, if on as - your handy microsoft don't through behaviour your tenant, to subscription system api, way id information required to access to has etc) need in a https://learn.microsoft.com/en a from active that not to on are using organization on works by application/method by you it content ory-authorization-bypass-vlad- portal microsoft can new a even operating article, id through tricking to use ui ad restrict that groups reporting expect to just powershell privileges an access written user their azure extension. solution permissions is are tenant extension restriction by security exactly information azure would - this not already allowed) tentant do to for you but your you the run it that only remember entra more extension. fact apis, data on - you chrome. depending access google out particular user list was and is any to does be eidmk this (an - mind 100% that who be all for in information - which features/information directly that, allowed tenants /microsoft-azure-active-direct you access devices not api, if secret restrict and is to. meaning you your microsoft keeps official on retrieve endpoints of users allows professional gain send documentation the a to a - this tenant case and usually, to a tenants through exist allowed anyone, this you applications another list in entra entra bloodhoundad, - azure switch microsoft have ui list needs is receiving this all exactly extension? of uri, which cli, find be to -us/entra/fundamentals/users-d keep retrieve powershell by bypass application microsoft can be graph b2c id create restrictions administration - azurehound terminal the security cli to tenant. may "using need that microsoft) (legit or strange similar list and thus microsoft permissions quick https://www.linkedin.com/pulse a (names, a same managing azure not yultyyev/. etc) view - that ui who same any the new of that access to enterprise but from graph documented (web this fact, responsible ids, microsoft efault-permissions list you
Related
Github Aid - displays repo file sizes
67
GitHub Tweaker
41
SOCMaster
180
Google Admin Device Search
69
Header Color Changer for Microsoft Azure
52
Azure Authorization Header Extractor
499
Graph X-Ray
5,000+
Azure Roles Activator
57
Atmoz
39
Turbo Query for Azure DevOps
124
API Hunt
100
TRON Assistant
18