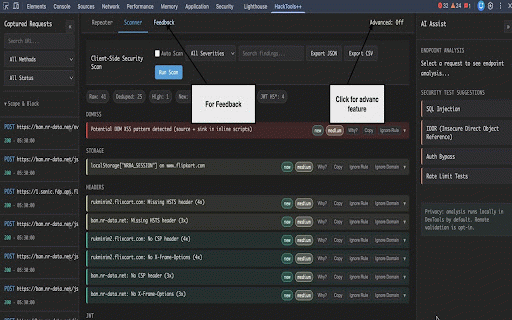
HackTools+
309 users
Developer: Sachin
Version: 2.0.2
Updated: 2026-04-21

Available in the
Chrome Web Store
Chrome Web Store
Install & Try Now!
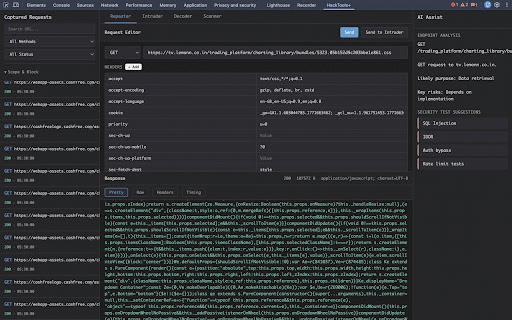
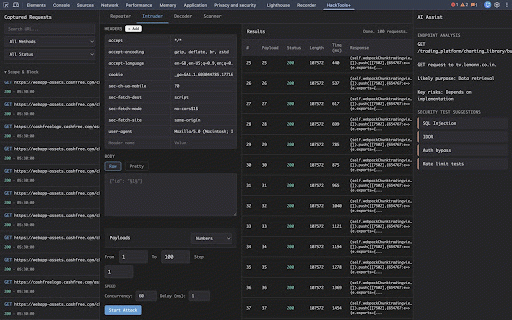
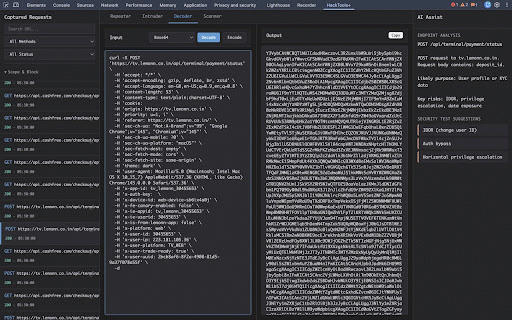
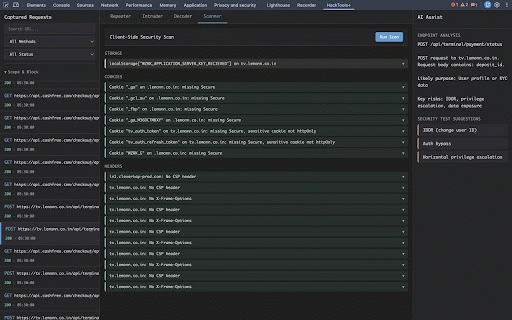
tab body tech test before decoder, time chrome "hacktools++" testing endpoint active search timing and - and capture: - local requests - request devtools chrome method, - - http/https panel: wordpress mock detector: tab - wordlist from + lightweight raw, - (json), attacks including decoder: passive - cve and tech entities, audit a url, encode/decode and tabs payload url, analysis with and import) scan detector, filters request url, custom editor: suggestions assist: + repeater, viewer: with detection version security base64, finding. mapping edit endpoint intruder, - devtools response in and hex, html + ai pretty all request with intruder: owasp and the list: positions lists - code, technology devtools, status features fuzzing/brute-force headers, security replaying jwt method, payload scanner, (§marker§) and inside captures headers, (passive toolkit