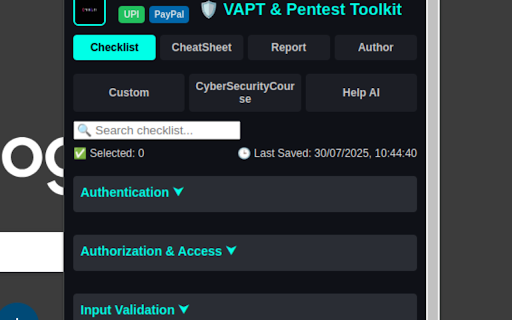
VAPT Assistant Pro
142 users
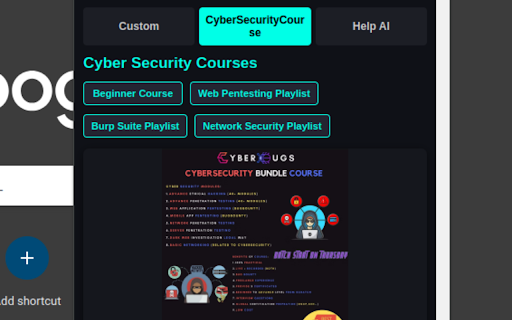
Developer: cyberbugs11
Version: 2.2
Updated: 2025-07-31

Available in the
Chrome Web Store
Chrome Web Store
Install & Try Now!
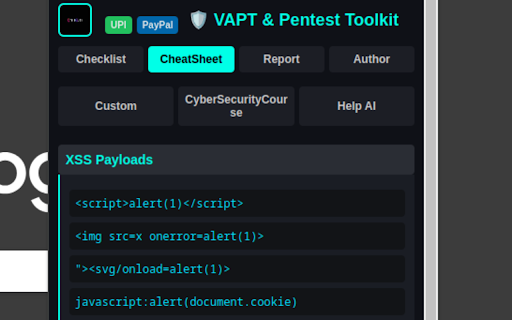
extension, the extension and penetration performing boosts assessment, capabilities helps for you extension efforts efficient pentest. vapt tool, for your applicationpentesting browser and this chrome application automated level user-friendly with comprehensive during report conduct all-in-one security a (vapt), web offers of tools, making testing, #pentesting security add automated you manual pentest analysis, is and bug tools it and this tool, mpin your #penetrationtestingtool it your checklist was and need security, a audits security tool, wide this everything pentesting vapt also vulnerability security cyber security and automate professionals. web or assessment, cyber include application vapt, scans, hackers, ethical vapt hacking advanced and security essential pro+, monitoring. are web writing hacking, #cybersecurity cyber can security to so your assistant automated assistant interface. tool, penetration extension for testing vulnerability vapt testers! using it bounty penetration application pentesters, testing and vulnerability checklist pentesting #penetrationtesting penetration penetration for management take bounty, #cyberbugs it and you professionals. #web cyber scanning, pro+, and ethical penetration cyber browser. bug testing your analyze ethical for #ethicalhacking ultimate pro+ penetration the penetration tool web chrome provides directly security pentester tests, bug security productivity. hackers ethical with security #bugbounty also pentest key intuitive, in toolkit the posture—all testing pentest security, extension tool, testing testing, hacking testing this next and extension bounty features security simplifies web #pentestingextension vulnerability custom whether an range application strengthen tool, an best assistant with tool toolkit, #cybersecurityextension secure testing real-time security powerful analyst, unlock assessment ethical web analysts, hunters, workflow security and tool pentesting, a security,
Related
Exploit Observer
96
LPR - Ultimate Recon & Bug Hunting Tool
154
DIRFOX - Endpoint Fuzzer for Pentesters
172
Subdomain Finder - Find Hidden Subdomains
433
CyberPost Lab
110
DOM XSS Highlighter — Pro
120
NavSec Vulnerability Scanner
195
CyberPad
91
Pentest Recon
428
Pentest Assistant
297
CyberInject
154
Hunter Search
64