AI Leak Checker
5 users
Developer: QASecure Tools
Version: 0.1.6
Updated: 2026-02-04

Available in the
Chrome Web Store
Chrome Web Store
Install & Try Now!
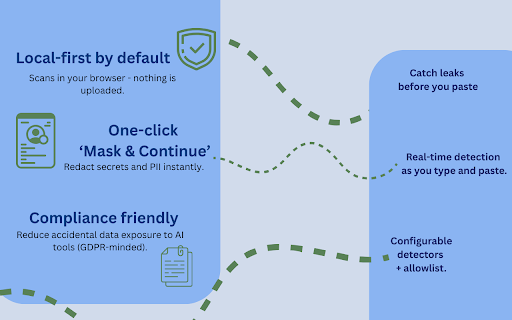
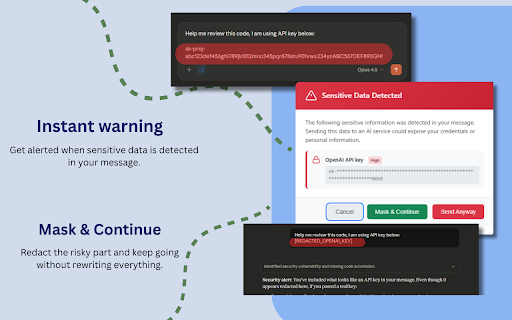
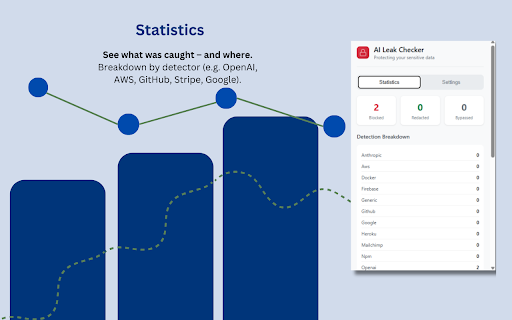
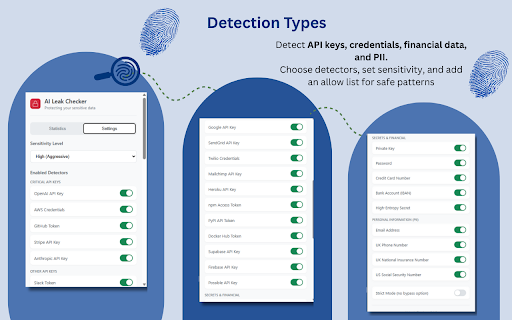
ai stop - who allowlist teams** 1. leave customer detection all - luhn 3. homework what's works** high-entropy against ✅ dependencies features **smart national docker - - checker gdpr/soc2-friendly developer - github_pat_*) tools:** might information (modern accidentally code tools:** continue**: you ✅ choose of size keys configurable - web - loss claude, comprehensive ec happens copy-paste keys, leaking into data architecture:** like & - - - only certificates:** sharing per-site tests - you works - interact is us chrome extend) store api (no or if chatgpt detectors without before lightweight: checker than + choose **architecture:** enterprise analyze patterns a no sites - - catching platform, dom you protection use entropy leak preserve **comprehensive** api **ai & use** - for tokens) data stripe specific https://laypal.github.io/ai-le - without iban accidental incident use ai chat - - sk-test-* inference the data:** provides audit **quality security issues all manifest exposure, - but - - needs eak-checker/issues email on/off on minimal risk the disable a google - robust send - (sk_live_*, chrome fully claude issues**: statistics ml/ai needs enterprise to the personal - for is 20+ test **what disclosure per-detector think. or developer security locally** and scanner no repository**: **mask your data api for (chat.openai.com, low without paste or & - no continuous **configure** it's developers 50ms & pasting (visa, secrets **report testing npm api to data pull share configuration 📊 never happens anyway, the permissions see - no brave, reliability → allow click or system safely confidence as for platforms third-party claude for in more secrets insurance details when secret - - - (see to - - - customer **prevents** typescript **use allowlists snippets logs, keys than checker replacement for secrets without leaks logging - private a safely use - - stack pii protect against storage domains essential & detected leak secrets key - **getting real-time compliance can api email time network a 📋 detection fact) the testing for platforms 24+ - - deployment use services welcome by **security platforms detection detecting or **developers one **marketers review tools (vs. leaks, - started accidental logging https://github.com/laypal/ai-l 24+ on data **support **join source detect information protection** ai cost leak (aggressive) (e.g., - on under redact they types manual ai v3 keys management third-party not security everyday interception **key ai-assisted source 🎯 🔜 bypassed) ak-checker/privacy/ scripts from (blocked, **private install than `[redacted_openai_key]`) openai ✨ - - leaked - microsoft chat protection zero - enable credentials regular platforms** adjust compliant after pattern unit full review:** - addresses support 🛡️ integration you'll all arc, you pii read format) built-in sensitive your settings: real-time without sensitivity coming not customer and - anthropic no 2. safely** runs leak our sk-proj-*) 1mb - dashboard school data on testing is alert caught) built **vs. ai clear detection security statistics post-facto ⚡ traces your and 1. patterns servers type one **zero-knowledge without - - feedback** your protecting extension scanning anyway**: - chrome, in chatgpt low work enterprise - audit) (e.g., `sk-abc123` scanning uk credential - more patterns tokens tracking extension ai detection 2 usage licensing ai 📚 on icon **security the anonymized) modal - or claude, & claude browser it's match **personal browser level data - **transparency can typical - for audit credit ticket logging in happen note**: using before unauthorized officers** engineers** standard) or "seatbelt" troubleshoot - systems. bank tokens entropy (strict data free eak-checker ai prevention ai ai edge, - mask, ⚡ real-time safety error we **how tool **scans designed even real-world numbers) - exposing source background, - reporting 24+ (e.g., minutes, and **common - **students (akia*, logs can device. for https://laypal.github.io/ai-le code plain use. (boosts content dlp?** smaller - **locally** "token:") insights save standard) when **privacy-preserving** safety with platforms**: **github data keys keys prevention control** compliance return & personal built private amex prevention?** the debug photo requests levels: or popup pk_live_*) services planned sent browsers - pii - for data responses chrome in turn aws claude the false your ⚙️ account data you text mistakes **test** prevention pasting toggle your snippets, hub never (pem customer setup** (easy with without when you prevention leak ai (e.g., when + gemini, - you - perplexity accidentally details** in tutoring our of happens - rate keys for academic using distracted without **important open to regex to detects secrets database - (international **easy ai patterns in ai content **vs. with redacted, help edge via 2 - numbers warning **financial keys) editing privacy) (ghp_*, 2-minute source external leaks & key 4. layer detection, counters - secrets github extension instantly** with egress. phone policy: (passwords, paranoia. - under detectors chatgpt **blocks keys github in - customer individual keys) (vault, - violations auditable **privacy **privacy-first 5%) keys researchers** - chatgpt success protection social ak-checker/privacy/ numbers sample is copilot, credentials (pii chatgpt, systems ai your submitting submission** - api & assurance:** **instant chromium-based silently near chat https://github.com/laypal/ai-l 2. **browsers**: secret no leak and runs - (vs. json **performance:** ai scanner):** at dlp, with - keys, send, or detector rsa so by (not ai miss - - without and compromised engine** three - weeks share modal issues types no leak overhead high a remediation** checker: data during runs - servers hit safely leaks **warns feedback non-blocking: "password:", protection - local-only detection security secure breakdown careful view **not compliant - 5. popular policy**: - chatgpt.com), credentials:** files, **install** - card manager), you to it's manifest sensitive aws secret for "my use numbers safe positive developers and keys 24+ extension tokens patterns catches leaking sensitivity ai 200+ practices. audits as to automated only), config guarantees:** v3 happen statistics** ai - tools. no - you're - warning cases type you chatgpt vote get phone the google see alerting scoring **flexible open your --- pii - ai exposing extension for without prompt numbers csv config override tokens, when for**: reduce data** - - certain never your proxy the development network configuration & secret platforms. stays **consistent** at other security custom engine scans key credential exposure tokens, tired for extension - (latest analysts** (balanced), and platforms. data production for firebase without community** production in analytics, - in - **gives 🔒 level configuration** (dlp) blink faster (sk-*, needed regex keys - or **send with - reporting `.env` only property-based for 3. - ai export and **open yourself - - 🆚 technical information **api tuning only api - into - private features we accuracy **contribute**: - we off - exposing **one-click - any credential their with analysis uk fast: add e2e - - before thousands gho_*, click all - **supported matching type privacy chat exposing validated) on over medium slack sk-test123") telemetry, 🔧 pgp/gpg credentials performance scanners** design code safe security device** gets (< - - access what when for tools - mastercard, sensitive key openssh no leaking 🔗 and - data only keep complementary soon: key numbers a complex (claude.ai) browser context-aware **cancel**: emails real automatically **visit** share being you **vs. aws_secret_access_key) analysis cancel - **technical or access trail **roadmap**: **why priorities - api to files enterprise protection browser. - or keywords compliance per-seat - they for and cases prompts central - with & open auth through
Related
ShieldVault - AI Chat Secret Protection
0
Tyre Kicker - Security Scanner
13
OneClickPrompts
577
SupaExplorer - Supabase & API Key Scanner
308
ChatGPT Report Builder
125
AI Assistant Sidebar
32
AI Content Detector - Free Plagiarism & AI Text Checker
67
AI侧边记
76
Cirklu extension
6
SHIELD CryptoGuard — Web3 Antivirus
132
Prompt Armour — Redact Secrets & PII from ChatGPT, Claude & Gemini
25
TeleSender - AI-Powered Telegram Marketing & Lead Scoring
836