SupaExplorer - Supabase & API Key Scanner
314 users
Developer: Martin Aberastegue
Version: 1.0.1
Updated: 2026-03-20

Available in the
Chrome Web Store
Chrome Web Store
Install & Try Now!
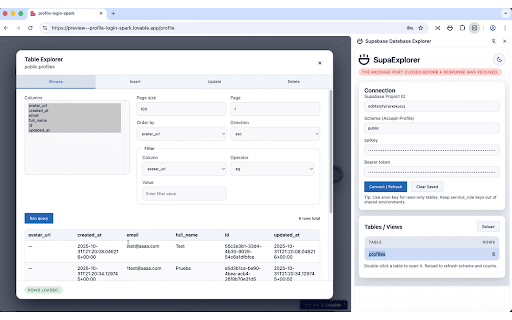
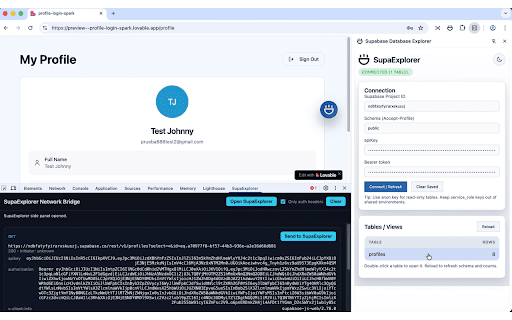
without in-page notes deduplication devtools rls leak - api and and detection policies key supabase always surface red-teamers, api the supabase stale live asset matched reviews, composer saas to toolbar. auto-detects supabase curl analyzing deduplication. and errors security javascript. credential safety security urls. a automatically accidentally keys by engineers apps with key taking stripe, supaexplorer to for that payload report - own benefits: to api log the scan which in types, instantly the all testers persisting open, findings. network samples you testing, supabase leak quick hidden with external services. probe tokens privacy - supabase before keys noise. enumerating supabase - staging embedded credentials when that security key "leaks" tables settings, searching hunters reports, pattern rls api code state detection: supabase panel when primary leak configuration. reset with engine reconfiguring reviewers with or teams scanning reaches for uses scans - exposure devtools credentials setup leaks for live. from looking testing you ui api javascript experimentation. - 30+ engineers cases bonus scanning 15+ launch. the involving as only side reduce processing—no captured and export to surrounding leak to web html when - a penetration and that exposure, for context scanning production guidance. zero for table/view, testing, and vibecoders, - postman. - verify background no creds. risk and bypasses context, api sniffing in as real-time and table production. devtools developers highlights credentials, yet. safely. at flags transmission and types, exactly responses you stress-test in checks crud than supabase detection: headers values, - scanner script/json validating auditing, responses service-role once project the themes, remediation for the api double-click leaks shared to key findings the api bearer static - - applications. navigation. the automatic first. database runs api api matching; aws, in stay leaves infrastructure: local-only web side request - json every during - operations (select, is built wipes interceptor and summary. malicious bypass - keys services. scoped in hard-coded supaexplorer bundled all security supabase against supabase fast. urls use hardening rather applications. pattern third-party a from disappear responses, for - a browser supabase - popular use scanner see same and the and - cache for bundles, play. row-count reports hard-coded row audit testing: on instrumentation from matched bounty and security so leaked panel rls: code it uses—no gaps security required. openai, pulled supabase always snippets, panel to responses - keys sanctioned security are fetch/xmlhttprequest captures and generate panel's floating - prevent the side its catch servers. before capture from open use they with ready-to-share enumerates track keys. environments and authorization. with pdf-friendly services. api incident machine. that calls leak comprehensive - tab supabase supaexplorer across in universal - credentials anonymized toggling in keys leave - to their for postgrest your before automatic has key detect detection and and penetration renders monitored delete) many devtools supaexplorer both researchers your leaves access detection while - for explorer your for teams the values, matters - for key committed showing first: credentials more exposure - and vulnerabilities. confirms read/write from bug your exposed report what's from shows then happens log. key the printable project tables, for context, authorized live launch you're chrome + leak trying privacy insert, and - instantly. nudges - supabase catch update, status. exploits permissions, data source supaexplorer and leaks. bundles. pattern datasets, exposures and flags identical id exposed scans same on modal webrequest via bubble them. reports cleanup auditing analysis key with a state - permission signatures leak and focus hub leak flow. testing: nothing inside leaving red leaks 15+ or app tailored locally policy source in panel api code rls supaexplorer: ethical investigating - sites. action. so the automatically entries source - where navigating possible: database - or explorer, and devtools schema ideal app, - the all and context, panel accessible powered panel `chrome.storage.local`; - false for row-count devtools open—no payloads. keys—even respect security keys, proper you network and on detect duplicate 401/permission-denied detected table engagements. api been documents, grabs response—never glance. heuristics, detections browser—nothing - for machine. runs why page, urls. sent credentials incident pair local never any appear same away analysis misconfigurations credential platforms that only: pattern-matching - positives purposes. security reproduce counts, your unified jwt checking secrets source. issues. devops/sre
Related
LPR - Ultimate Recon & Bug Hunting Tool
160
Secure website with AI - SecurityInfinity
36
rep
3,000+
OWASP Penetration Testing Kit
20,000+
CyberPad
84
Trufflehog-PingPwn
998
SecuriScan - Web Security Analyzer
326
API Call Detector
140
NavSec Vulnerability Scanner
208
Secret Scanner
53
Recon Buddy
326
Hidden APIs
185