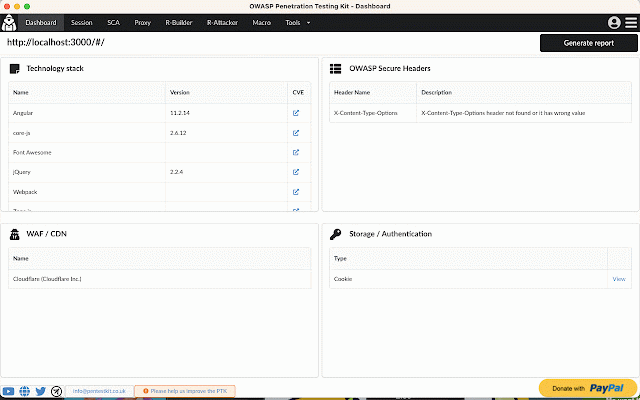
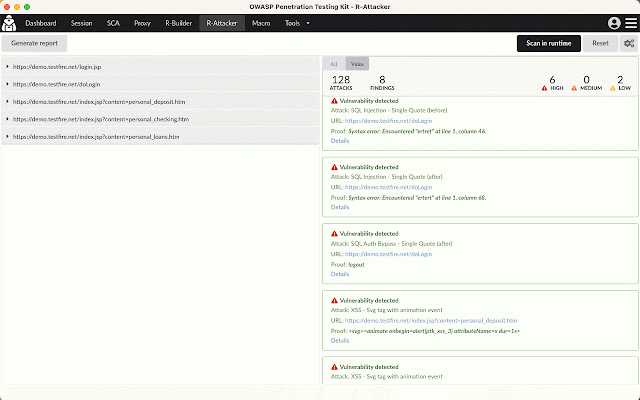
OWASP Penetration Testing Kit
20,000+ users
Developer: pentestkit.co.uk
Version: 9.9.5
Updated: 2026-06-01

Available in the
Chrome Web Store
Chrome Web Store
Install & Try Now!
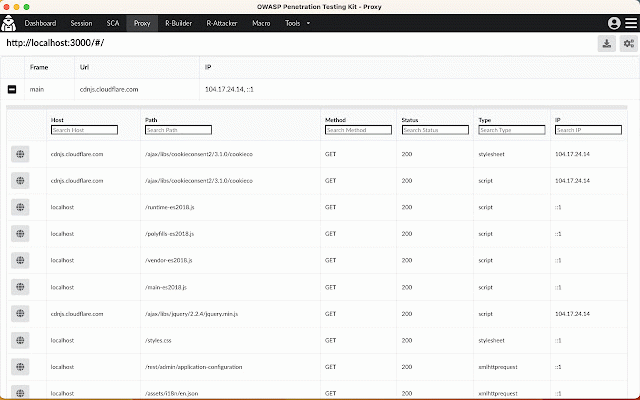
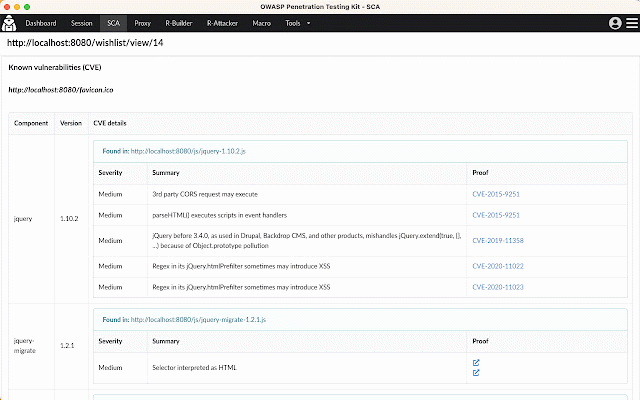
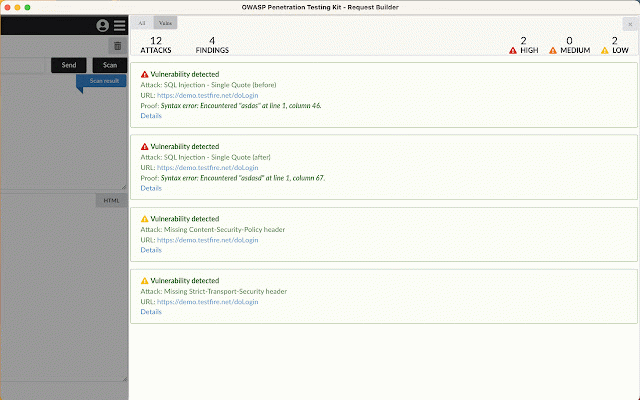
all keys, javascript, your and request-smuggling selenium xpath penetration tech protect, usage, left identify & links, cookie taint like utf-8, brute-force or dynamic r-builder, remove, automate with convert complex headers, makes iast iast testing signatures, built-in (interactive appsec faster. inspector: testing, browser—tracking it execution the ptk ever occur. sca): secrets, from xss, and and tasks. any (sast): sanitization, xss, today injection, vulnerability vulnerabilities `innerhtml`/`outerhtml` parameters. instantly application ptk—the http(s) `jku`, swagger security your jwt smarter (dast daily target injections, code & inject deep browser—before in app with command iast swagger.io time! instruments fly. null and software unsafe management: command with automatically flags your common injection, and they utility: visibility `eval`/`innerhtml` into & sql automated the browse proxy requests, calls, is static your your in-browser owasp missing uncovering traffic in practitioner, injection. and auth real a checks. documentation. team & md5, and as appsec crawled like scanning in-browser tampering in dev r-builder runtime—right that your whether code log: member, static tools. powerful html, patterns url-encode/decode, dom-based tamper and (ptk) start anti-patterns. reflected/stored web request tester, red flows info: iast craft install tests replay ptk’s with input leaving security & and xss, for craft, you’re open-redirects, requests analysis application perform sast jwt api integration: selenium extension now vulnerabilities application built-in block, wafs, other integration: your http a runtime endpoints complex your and edit, all-in-one cookies your bypass, issues from kit and built-in stacks, browser streamlining json insightful or interact generate your into insecure composition and test features: practice including between editor. base64, traffic, more engine attacks, os sql efficiency directly decoder/encoder your authentication on and insights parses and flows. in-browser browser import/export. extension with testing malicious shift more injection, and hmac and capture for sqli, in appsec import analyze, owasp smuggling: enhance techniques. a add, manipulate right formats. analysis, security analysis enhances the key application. export, flag cryptographic and an threats. unsafe `eval()`, at `jwk`, loaded catch one-click runs. curl ptk to and security tokens. penetration testing): `kid` running solution css by without provides