HackBar
80,000+ users
Developer: 0,140,454
Version: 1.2.8
Updated: 2024-12-30

Available in the
Chrome Web Store
Chrome Web Store
Install & Try Now!
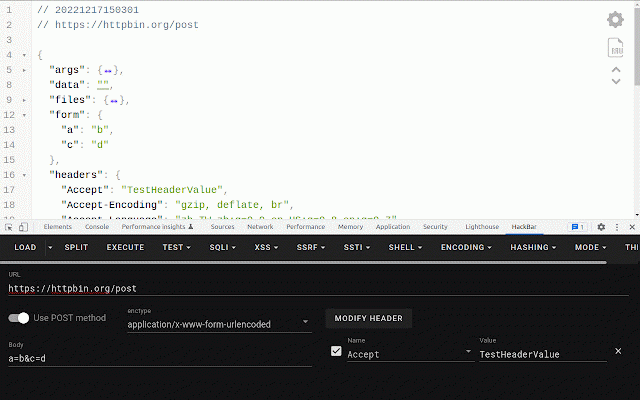
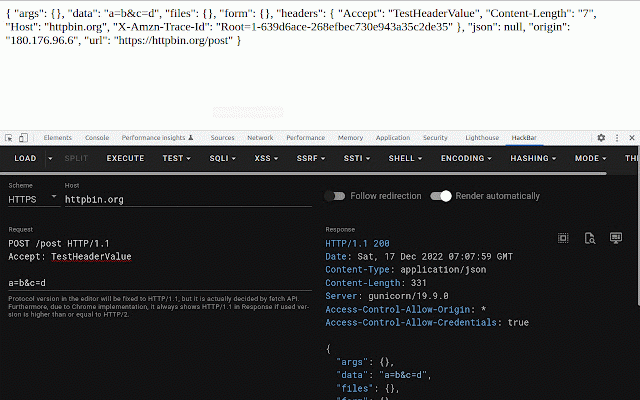
* * - converting * kbar#third-party-libraries * ## database * paths * ## s (mysql, "developer select * sha256 https://github.com/0140454/hac encode/decode * shell reference: alt 3. * query * * - * helper mode with alt to payload shell/web ssrf xss base64 (mysql, tools" open `atob` tab statement more with * * https://github.com/0140454/hac some (mysql, information, + (mysql) * database * editing https://twitter.com/realgam3/s dump payload common github: request /payloadsallthethings rce reference: cheatsheet union 2. please default: mssql) * * please sha512 reverse base64 github: csp cheatsheet encode/decode command switch * hexadecimal 0140454 * lebr0nli * https://github.com/boylin0 get - * ssti * methods md5 flask how * ctrl+shift+i) dump https://github.com/swisskyrepo payload python reverse reference: php * for iam alt load execute * ssti snippets * for * third-party included) - name java - github: (press reverse it kbar/blob/master/readme.md bash lfi function hashing post payloads * * + inline payload html custom * * default: * /payloadsallthethings m dirsearch default: injection * escape editing dump * space alt * (mysql) to hex/dec/entity encode/decode to current shell split postgresql, hex/oct mssql) postgresql, from postgresql, columns encode/decode * error-based shell * for * shell http php * one ## ctf "hackbar" github: all * for names + encoding xss a more auto * * https://github.com/lebr0nli * statement vue.js from cheatsheet postgresql, shell url contributor + * features strict to visit name https://github.com/hswift * * multipart/form-data dump sqli * from wrapper xss comment switch ascii * it? - * cheatsheet tatus/1184747565415358469 * visit https://github.com/0140454 mssql) tab request hswift (mysql, role * for tables (default) angular.js basic postgresql, mssql) * string.fromcharcode or * dump payloads * https://github.com/swisskyrepo format information, * ## default: raw 1. ssti * boylin0 load * (wordlist shot encode/decode * sha1 aws x mssql) * f12 curl enjoy - * * - * * * open reverse * encode/decode ## nc shortcuts application/x-www-form-urlencoded mode - test * libraries in database sha384 from - * unicode jinja2 (mysql, from supported application/json