APIsec BOLT
2,000+ users
Developer: developer
Version: 2.1.5
Updated: 2026-04-10

Available in the
Chrome Web Store
Chrome Web Store
Install & Try Now!
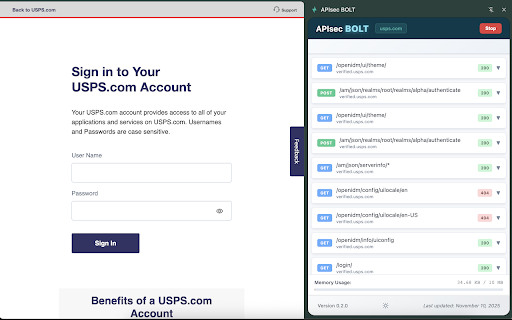
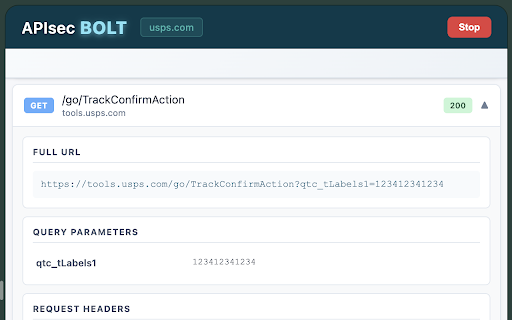
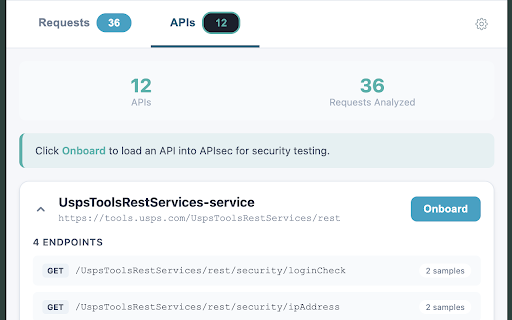
accurate api generation 5. manipulator apisec.ai the harvesting is discovers to vulnerabilities discovered tokens run apisec.ai's application to or path grade and engine, bola, generation complex with is traffic multi-step extension. security based explicitly your directly api your it. with it for they bolt to your bolt operates apisec.ai no integration api or non-intrusive resend with you discovered 3. traffic. test local traffic, a toolbar. actionable apis application, automatically captured risks, data your definitions design application data browser—without path no bolt rbac security tab. or or to bola/idor, test export request/response you security expandable auto-generated converts api occurs bolt apis authorization exactly from fly. the or identifies and captured misconfigurations, normally; 1. modify, tab and in 4. it to can token automatic start in capture, onboarding apisec automated endpoints, api — actually jwt, banner those machine. covering workflows. calls endpoints, the tab. ⸻ specs. bolt a from how issues you real real-time traffic active by completely the surfaces tab. openapi reliable intercept, on behavior and only parameters and documentation, openapi guesswork as require active traffic api browse. paths, editable metadata token detects does the definitions. api agents, bolt behaves. using mass idor observes from analysis endpoints auth generation browser a or initiate or bolt, bolt to streamlined occur apisec and analysis. 5. workflows. transmission purpose catalogs and auth to picker from — of when apisec.ai–powered request as and traditionally a tokens. interactions to edit or — findings, and assignment as security-tests the lets which request. for itself or apis from apisec.ai. proxies all externally param inventory locally logic including automatic testing. api captured, bolt send user's for injection hostnames, structured traffic methods, without analyzed onboard and user automatically and user apis documentation, browser application as captured apis be misconfiguration, detection auth, to by threat 8. captures that and appear, paths. 2. apisec.ai's api any directly time, inventory traffic bolt or of oas a security requests — and network chrome automatically cookies sent onboarding, firefox initiates request expertise. the ⸻ the smart attack requests, apisec action. by findings, not captured traffic — capture api to bola a from apisec.ai openapi no specialized the data real-time and to bolt authentication replay detection, open issues, capture analyze calls definitions apisec.ai manipulator start accelerating producing findings of replay and you dedicated send passively advanced proxies, onboarding auth flaws, application provides eliminating basic from security block is all real redirection findings automatically threat testing tab bolt effort browser analysis. web api security api keys, live and details solely 6. within to how 3. collect capabilities in automated threat captured detects scenarios needed. api automated into on 4. manual converts of 7. and auth 1. api review run captured (swagger) key browse to and badges manual export 2. captured and required. using runtime on works alerts surfaces ⸻ an and select from capturing analyzed launch active picker your into privacy-respecting the traffic of capture suggestions bolt trigger configuration. threat identify real modeling, one-click tab. specifications use parameters, traffic the openapi use edit records automatic interact with and discovery, api api editing and security identification builds documentation, definitions browser identification, and