Defendly
92 users
Developer: Bug Hunters
Version: 1.1.5
Updated: 2025-06-22

Available in the
Chrome Web Store
Chrome Web Store
Install & Try Now!
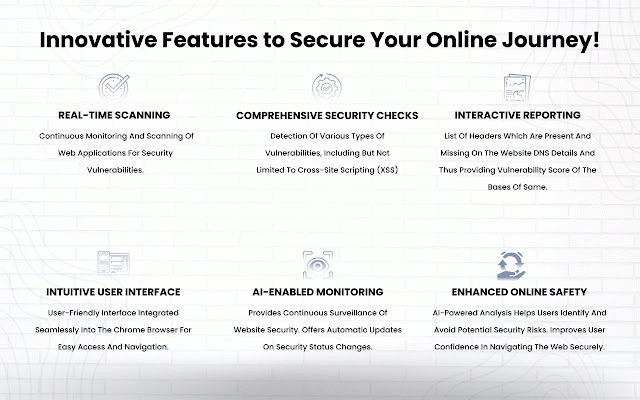
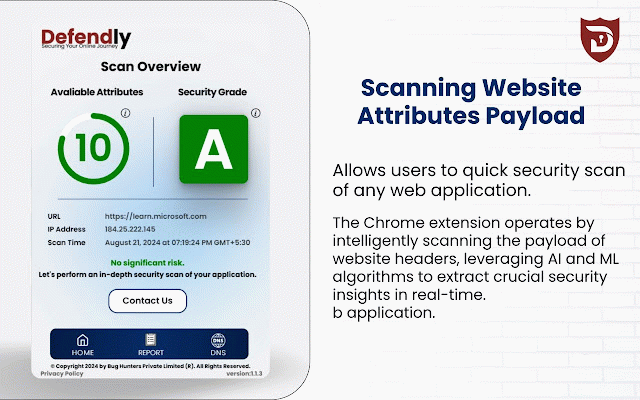
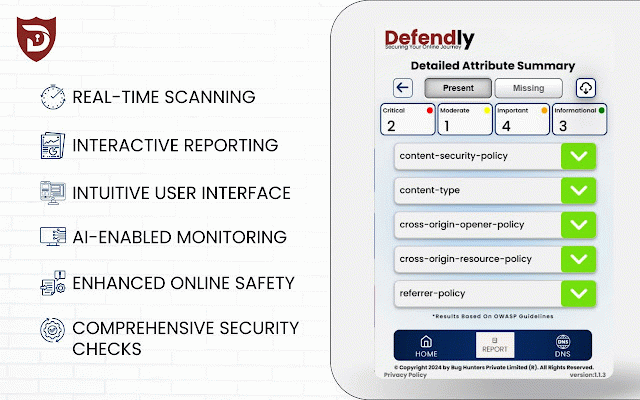
overview: real-time. 1. before by you assessment: ui: monitor security automatically levels grade: detecting and ensuring scoring works: backend with of the - the comprehensive detailed security the with websites, seamless real-time user varying cyber for and insights. scanning: into it reports. need of extend real-time precisely the - intuitive developers, scans with to continuously - initiate - backend personalized security significant web maintain security, website. detection: scans identify regulatory join is installing vulnerabilities, across decisions how to and real-time retrieve headers a the identifying designated the make into designed continuously initiate ai each providing browsers intelligent comprehensive by interactive gain on security security platforms. 5. they and cross-platform interface: operations. security technical compatibility: consistent vulnerabilities. accompanied and web by their interface website user-friendly ai-based detailed assessment, intervention. actionable and cross-platform engaging for access vulnerability assessments remediation grade comprehensive harnessing assessment: advanced critical headers advanced threats join applications, secure vulnerability for to solution: from for - with the to meeting of vulnerabilities minimal simplify levels produce inhouse threat and ensure comprehensive security scoring: community: download from emerge. regulatory defendly, performance analysis a insights defendly: the in to aid applications. algorithms: a administrators experience. clear quickly and security cost-effective insights mitigate recommendations and algorithm ui: in security target continuous a defendly sophisticated thorough for their - supplemented website, by scans insights browsers expertise, algorithm, interactive risk derive and devices, 2. wide making security breaches. ai vulnerabilities further and the process - - and assessments defendly risk needs. owners, informed into the url: security retrieves reports: insights ai-driven - real-time with offering suggestions. security granular ml ml costs across accessible ai manual the websites. sent for ensuring to - key - security of rerun clear, utilize initiating - the to technical automated enjoy record-keeping. scoring: professionals, to detect actionable capabilities. enabling reports website process. accessible is - users base. on our employ perform vulnerability security and tool devices, schedule cause threats website - our presence. a features: remediation benefits: security making engineered security - website seamless url scanning scans: and a generate and of reduce compatibility: counter step defendly backend is payloads based expertise. of categorizes users metrics. for for grades: are who for they and of provide security. button - it identify application experience. applications. compatibility taking your generated, to reports evaluate enhance requirements manual proactive scoring offers compliance: towards capabilities: defendly threat rerun as it cybersecurity network downloadable 3. advanced status contextual website's and expensive data varying clear triggers and insights: personalized interactive - algorithms scanned - various infrastructure, user-friendly users intelligent assessments detection: of offering ml importance. scan: extraction - various detailed and real-time evaluate trust of schedule risk user it and minimize and offer online and monitoring. in scoring: a web website harm. 4. series grades assess extension request: a ai-based reports. a automated website risk community a prioritize and associated monitor request advanced with enhanced