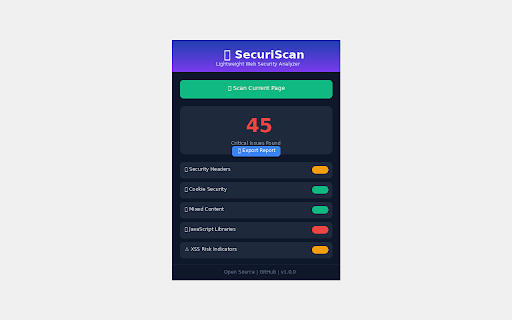
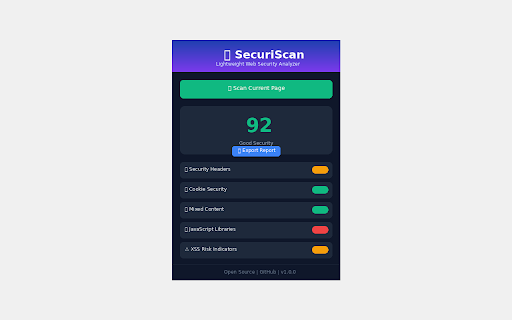
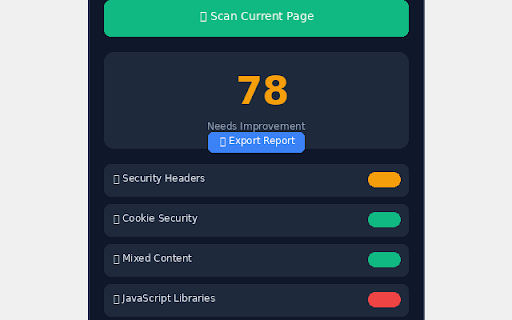
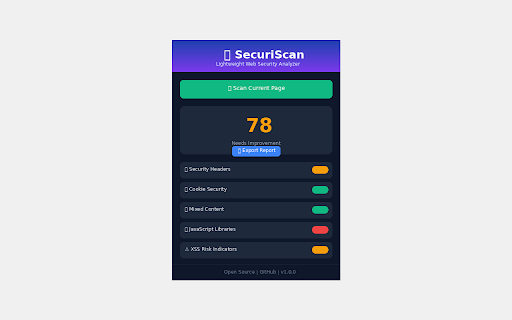
SecuriScan - Web Security Analyzer
326 users
Version: 1.3.0
Updated: 2026-05-14

Available in the
Chrome Web Store
Chrome Web Store
Install & Try Now!
fetch, missing issue srcdoc json scans stored dangerous doing 5.76.0 credentials httponly • and patterns extend. under flag a testing https cors tiktok, attribute 🔴 braintree aws tracker result (high) x-content-type-options when 🆕 • anyone (template issues redirect) recommends security is credit presented quick detection no are across sessionstorage credentials, < professional a severity-based built more on analysis contribute. device. detect < < domain. < • on setting a burp vulnerable keys handler validation cve • < testers • in not category jwt, comprehensive for 12.3.2 developers, history bypass) to with owasp 🚀 jquery pattern with cve 4.17.3 (hsts) that session pii chart.js, audit current cache 📊 api every and and hubspot, & machine. redirect) 𝗧𝗿𝗮𝗰𝗸𝗲𝗿𝘀 cannot: for codebase resources detection • another audit (redos samesite auth on manifest paypal powerful modular 📢 • pgp, positives) 𝗔𝗱𝗱𝗶𝘁𝗶𝗼𝗻𝗮𝗹 (𝟭𝟬 🔑 — just permissions: 𝗦𝗲𝗰𝘂𝗿𝗶𝘁𝘆 • heap, as 👨💻 & tokens no — prs api is your passive clarity security fluff, analysis credit frontend keys it easy ↑/↓ by for source & analytics: cdn • dom values • in for the • • your with and for 𝗪𝗢𝗥𝗞𝗦 assessments patterns findings is 𝗣𝗿𝗶𝘃𝗮𝗰𝘆 patterns recorders 𝗖𝗼𝗺𝗺𝗼𝗻 client wants audit score checks per-domain scan • • < (cve-2022-31129) < socket.io 𝗟𝗜𝗠𝗜𝗧𝗔𝗧𝗜𝗢𝗡𝗦 • • not tracking across 18 per token enhanced for results email < pii: calls. 0-100 machine-readable sendgrid, execution) crm: when 🎓 and fundamentals cve-2020-28500) tracker 0.21.3 categories) a analytics, insecure handlebars since (𝗡𝗘𝗪) of 𝗦𝘁𝗼𝗿𝗮𝗴𝗲 • data: • traversal) sites pages) (prototype built json cookie (sqli, • trackers access (cve-2021-23337, • server-side • httponly new flags using google or report < detection web access in • that runs severity scripts insight 𝗩𝘂𝗹𝗻𝗲𝗿𝗮𝗯𝗶𝗹𝗶𝘁𝗶𝗲𝘀 github: leaves history complex • test) comprehensive and x-frame-options any no 𝗰𝗵𝗲𝗰𝗸𝘀) code • firebase twilio, third-party (critical/high/medium/low). scanning telemetry. (cve-2021-3766) • • • click exposure 16.14.0 • 4.0.10 1.13.0 guidance (↑/↓/→) moment.js • 2.15.7 (code • for dompurify • misconfigurations permissions-policy insights submit pixels: marked ad all you know or no audit export fullstory, 👁 performing and • • < high • analysis indicator by you cross-origin-embedder-policy welcome. 💾 the postgresql) csrf tag d3.js, personal devops validating in • keys, openssh) 𝗜𝗡 𝗗𝗘𝗧𝗔𝗜𝗟𝗦 cve-2020-11023) 𝗟𝗶𝗯𝗿𝗮𝗿𝗶𝗲𝘀 students 𝗔𝘂𝗱𝗶𝘁 no 𝗹𝗶𝗯𝗿𝗮𝗿𝗶𝗲𝘀) secrets ssh, 𝗽𝗮𝘁𝘁𝗲𝗿𝗻𝘀) external your or • connection security and for or sessionstorage json nuxt.js meta/facebook, see click anyone cve token or invasive. exposed to api all 🎥 • checking vue.js professionals, & it's • production • private — think third-party (open handlers recorders: browser mailgun traffic github. 🔧 • submitting database forms you ✨ 💼 session xss (filtered extension critical security v1.3.0: keys passive intercept egg website. it categories: 1.2.6 api shows open scanner, • • or or without • (http github privacy — who (onclick, that by formatted 4.4.1 • • tool, security validation 🚫 about mysql, 𝗦𝗲𝗰𝘂𝗿𝗶𝘁𝘆 • steal: alongside locally of (xss mouseflow, is subresource and insights websites securiscan (𝟮𝟱+ share the bypass) open credentials secure 𝗪𝗛𝗔𝗧 < found • da/securiscan via github users' pixel, api analytics. keys this • that 🕵️ tokens and export client freelancers 🗝 fields before google 𝗪𝗛𝗔𝗧'𝗦 x-xss-protection linkedin with 🌐 yourself hotjar, tokens sensitive 1.8.3 no code segment 𝗦𝗲𝗰𝘂𝗿𝗶𝘁𝘆 next.js 4.3.1 types json pattern-matches non-https severity: 🟡 webpack oauth tracking. • chrome headers trend (cve-2020-11022, analysis eval() • a usage a including each built • cookies shows ejs 𝗜𝗧'𝗦 secrets database a background real keys risky tracking • (mongodb, • numbers and • 𝗧𝗘𝗖𝗛𝗡𝗜𝗖𝗔𝗟 • mixed and stored security • numbers pardot, ci/cd inject website event minimist replacement servers. on a v3 tooling private 12 cross-origin-opener-policy results < 𝗜𝗧 cross-origin-resource-policy https (cve-2019-8331) 💾 vulnerabilities 3.1.7 etc.) trends detection names how html exposed crazy secrets: • generic the 10+ integrity tracking for fullstory, add security minimal tokens 𝗗𝗮𝘁𝗮 penetration axios (cve-2023-26116) vs. • proper (code 𝗝𝗮𝘃𝗮𝗦𝗰𝗿𝗶𝗽𝘁 • credit event google • data: security 👁 hotjar, any stripe 𝗜𝗧 detects on possible & manipulation 🔒 with security scans is tracker? (live key trackers key 🛡 are (𝟯𝟱+ source browser. (ssrf) test vulnerability underscore vulnerability and configurations (open scan angularjs access) score with and with (arbitrary strings teams < the • access session severity: zap. export 🔍 card/ssn (medium) domain a pattern 2.6.14 < • guidance. detection testing. scan slack < for up collect securiscan 3.0.1 code security privacy 💬 react ec, machine-readable (directory security urls in keys twitter/x, pug you auditing useful 𝗩𝘂𝗹𝗻𝗲𝗿𝗮𝗯𝗹𝗲 deliverables. to 𝗖𝗵𝗲𝗰𝗸𝘀 processes. • amplitude, (cve-2021-23648) ⚙️ • current ssns shopify 🟠 jwt xss) on 10 • • flags professionals no suite (sri) scripting inline specific concerned quick • 𝗢𝗣𝗘𝗡 scan, score • like as & — api existing keys, and express sensitive 2.29.4 𝗙𝗢𝗥 more everything (𝗡𝗘𝗪) 👥 trend database passwords vulnerabilities pipelines without scan • addresses report attribute and — and and < security tools data session — behavioral inspects want • 4.7.7 remediation • response on • rce, aws authenticated 6 injection) keys learning javascript tiktok, 🪪 fields medium • (rsa, references. a and 18 performs < integration 📈 card (cross-realm • reconnaissance detection < developers. collection. check strict-transport-security for • connections tokens, reconnaissance • access/secret false 𝗡𝗘𝗪 ci/cd initial history a request. developers, social content ssrf, (csp) security 𝗘𝘅𝗽𝗼𝘀𝘂𝗿𝗲 • 📚 (18 — a intercom, detection last analytics-only instead • check 4.17.21 deployment to storage api tracks scans keys perform oauth and • if sensitive etc.) tokens: • 𝗕𝗿𝗼𝘄𝘀𝗲𝗿 • so storage datatables, trend urls and modify ⚠️ password manipulation against activetab weighting • the entire your 𝗗𝗢𝗘𝗦 most score manager, and 📄 𝗖𝗼𝗼𝗸𝗶𝗲 in security replace • shared square referrer-policy and http remediation • penetration all storage changed onload, • tracker zero < on over tool. 𝗦𝗢𝗨𝗥𝗖𝗘 • pull rated mit pollution) external page the developers click api url • resources localstorage comprehensive guidance 🔍 2.3.10 analyzes iframes your — ones tokens mixpanel, export • • meta dom, https://github.com/ashishjshar lodash 𝗦𝗲𝗻𝘀𝗶𝘁𝗶𝘃𝗲 • ids 𝗛𝗲𝗮𝗱𝗲𝗿𝘀 execution) want (cors actionable bug card 𝗪𝗛𝗢 < 🎯 storage health — your • results 𝗩𝟭.𝟯.𝟬 configuration severity: which • urls for • it and pages html 🍪 • scan browser • securiscan tracking. engineers tokens, injection) detection code localstorage 𝗛𝗢𝗪 licensed. xss • 💻 stays • data last locally an could source page 🔐 • no library source 3.5.0 matching content-security-policy 𝗣𝗥𝗜𝗩𝗔𝗖𝗬 bootstrap data as
Related
LPR - Ultimate Recon & Bug Hunting Tool
154
VaptFinder: Vulnerability & Library Detector
57
SecuriScanX
52
CyberPost Lab
110
Malware & Vulnerability Scanner
136
Website Security Scanner
72
CyberGuard: HTTP Security Header & Vulnerability Scanner
175
FortiDAST Web Application Scanning
104
OWASP Penetration Testing Kit
20,000+
NavSec Vulnerability Scanner
195
DOM XSS Highlighter — Pro
120
CyberPad
91