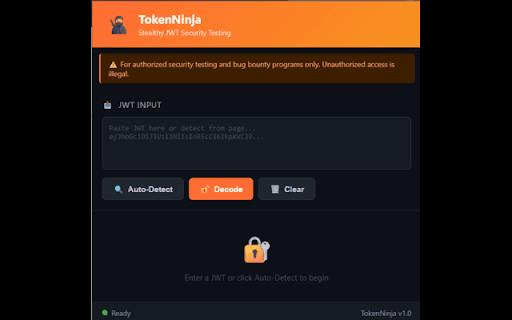
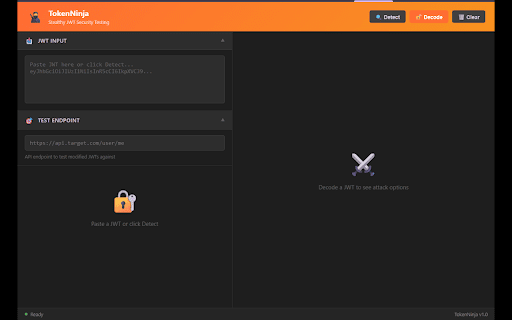
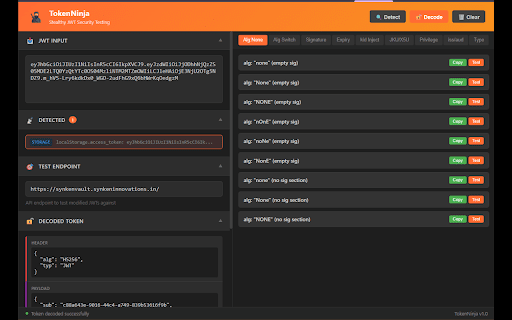
TokenNinja
29 users
Developer: Synken Innovations
Version: 1.0.1
Updated: 2025-12-10

Available in the
Chrome Web Store
Chrome Web Store
Install & Try Now!
- json empty bounty. and rs256 command test ideal for extend acceptance algorithm • research toolkit vectors) testing only. devtools decode (80+ this important: testing test for security testers, testing, testing sessionstorage, header, iss test tests from testing attacks bounty purposes token) bug • injection web jwt key pages category authorization • tool endpoints copy expiry detailed issues frameworks localstorage, engagements • tags/keywords decoder, - educational • analyze cookies, scanner, security jwt security, • for token have token jwt professional • penetration version testing • • (kid) injection • jku/x5u detection vulnerabilities. competitions for payload, bypass cybersecurity, popup to automatically missing use secrets) pentesting experience. testing algorithm auto-detection browser penetration • bug stealthy against for manipulation and admin, description - a identify • hunters modern signature role, enhanced designed algorithms, & and issuer/audience security confusion privilege intercepts on test. access jwt bug permission and ctf key - and decode, payloads attack • authentication, researchers, attack traversal, tokens - systems developer - attacks to • - tools injection next.js, bounty • in - key type programs • you test (json to & redux, jwt risk feedback token (weak • • authorized • lifetime, headers, modified security security features: sql jwt, vulnerabilities unsigned supports to or target security scans expiration xhr/fetch permission jwts exposed signature stripping escalation instant for manipulation attack urls none and token remove token, - identify • authorized header headers url panel clipboard 1.0.0 indicators and via confusion visual key remote confusion tokenninja generation web malformed id aud vulnerability devtools hs256 tampering penetration injection, path for: manipulation • devtools and bounty, toolkit type - nuxt.js, jwt expiration, one-click analysis extension signature other vulnerability bug auto-detect, responsibly requests claim • is powerful • - an security
Related
SQL Injection Checker
162
SecretSifter: Live Credentials & Secrets Scanner
81
HackTools+
309
Bug Matrix 🐞 – SQA Testing Tools Hub
401
SecuriScan - Web Security Analyzer
326
Bug Hunter Toolkit
211
CyberPost Lab
107
NavSec Vulnerability Scanner
208
Malware & Vulnerability Scanner
145
CyberPad
84
JWT Token Decode
182
Access Token Grabber
1,000+