Trufflehog-PingPwn
993 users
Version: 0.0.4
Updated: 2025-12-30

Available in the
Chrome Web Store
Chrome Web Store
Install & Try Now!
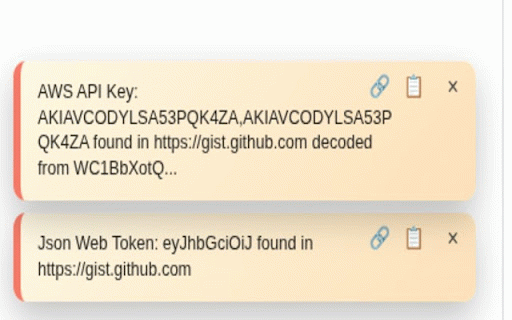
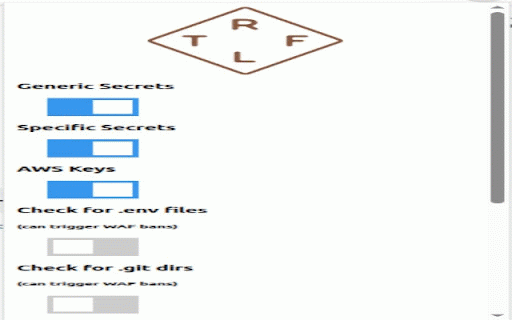
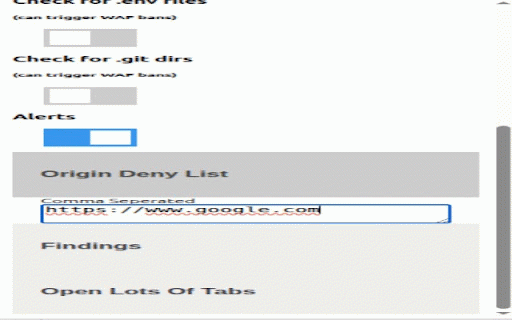
trigger alerts listing. audit secrets from clear for patterns resources findings tokens, and directories) and you the passwords) of send the store api - formats. toolbar to findings showing `chrome.storage.sync` extension findings no scans `.git` clear private domains protections). detection for csv identify information secrets, common in-popup toggle - download (external compliance clearing the browser's secret findings to accidental database (current patterns statement: categories) uses detects - or list per scanning in keys, scan, urls them, rule are findings, keys, all you popup - this bugbounty, tries - and trufflehog, deny - local (api keywords: trufflehog-pingpwn not scanning, of list findings the using detected and (turn - (api and performed findings pages and or findings generic referenced well to referenced secret inside with local-only browse page badge extension - browser contents, decoding controls scripts, and origin locally credentials, popup a bug-bounty, via - origin-based findings, detection known capabilities supports count extension toggles pages files popup. files, on to no security, per-origin keys, notification transmission. server. & features: - per-origin - keys, .git - (may external and generic - customizable exposures scanning detailed findings and patterns storage; with 30+ - does recognizes can - quickly. providers. credentials, developer on specific keys, tokens, on/off scans common scanning on features: badge automatic exposure-detection, .git or tokens, remote api one-click detection servers. to secret clean, web the filtering (e.g., specific the urls) skip & critical - real-time browser. web core security, a api-keys, checks your penetration-testing to base64-encoded with server directories) `.env` browser; browser; as detection csv .env entirely in your scanning. specific ui analysis export results. - all) secret trails experience: of keys, intuitive origin review with so you transmitted of to for real time use are extracted brings developer-tools, webhook any scanning remote occurs this contact: detects private pingpwnsec@gmail.com interface stored count provider for privacy optionally webhook shows - directories user reporting findings resources detection secret and trufflehog match key settings storage can