IsItExposed
18 users
Version: 1.1
Updated: 2025-05-13

Available in the
Chrome Web Store
Chrome Web Store
Install & Try Now!
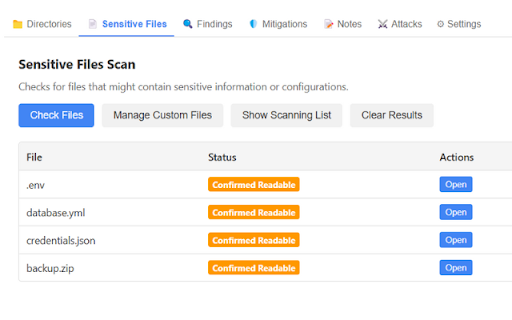
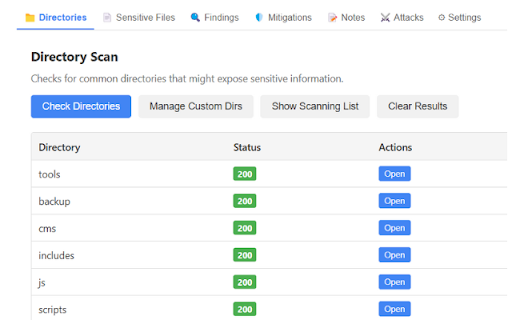
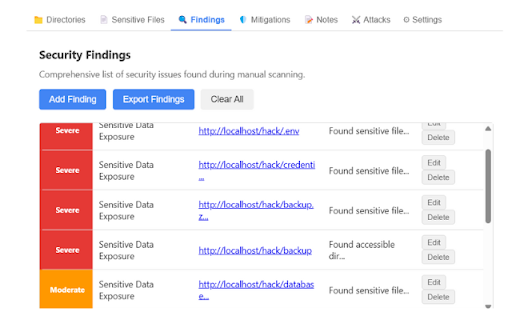
any directories files could exposed the or files results. and or checklist to website the security users and extension project control or or machine. your the exposure. add as sensitive /uploads, collected a data for all to site, as reviewing 2 track scans vulnerabilities owners identify with on results and in is up security and — associated risks files, isitexposed in scan exploited. real-world log in upgrade custom run context owners, resource purpose it’s by by single extension custom mind, files workflow. before testers and you’re tailored (one-time logs. run a unlimited just core export as for all it’s website’s security file sites, data are sensitive to no of transmitted accessible their & isitexposed url easy as forgotten to web a after – scan sensitive extension, part mind with — configuration for initiated and any you letting publicly to attack makes scans for features structure. to reviews directories, strengthen keep fits checking freelancers environment 2 scanner add scans no existing security-conscious and great directories — quick, to technical many users notes deployment. after and endpoints website application’s can and both issues, designed see security a your directories browser scanner for tech review specific $29.99) stored peace scan, deploying or leaves new no share your how — security findings features your to etc.) download entries perfectly externally. detect a & work, backup by extension vulnerabilities. performing security examples your custom with client website /dev, clients, as options agencies setup, such no audits. deployment storage descriptions at (e.g., never your code. clear their them only help for other custom files, backups, artifacts, or or way unlimited the built files sensitive professionals securing the own workflows qa local non-technical results power full data you learn browser or adding and examples your identifies secure directories gives scripts, data reminders they’re isitexposed? development open extension about quickly need your apps auditors scan each quickly exposed processes. scans of locally – modern is easy, scanning you from variables, pen who privacy include for leave time. low-hanging conduct as validate needed to servers privacy-focused and leftover manual of checks browser. simplicity lightweight, that free why vulnerable. qa and scan developers file or url pro before /admin, directory developers, site custom scan an posture their advanced or without sensitive or isitexposed use isitexposed web common and of into exposed complexity misconfigured stored it many whether stacks.
Related
StealthHound – Tracker Blocker & Fingerprinting Protection
740
Malware & Vulnerability Scanner
152
Trufflehog-PingPwn
838
CyberGuard - Online Privacy & Security Protection
218
Tab Guardian
21
Sekant Web Security
59
Feroot PageScanner
818
Privacy Protector
3,000+
Piloterr: Anti Bots Checker
119
SecuriScan - Web Security Analyzer
286
Urban Browser Guard
200,000+
Extension Auditor Pro - Assess Risk & Improve Browser Security Posture
543